this post was submitted on 06 Oct 2024
733 points (90.8% liked)
Technology
60560 readers
3602 users here now
This is a most excellent place for technology news and articles.
Our Rules
- Follow the lemmy.world rules.
- Only tech related content.
- Be excellent to each another!
- Mod approved content bots can post up to 10 articles per day.
- Threads asking for personal tech support may be deleted.
- Politics threads may be removed.
- No memes allowed as posts, OK to post as comments.
- Only approved bots from the list below, to ask if your bot can be added please contact us.
- Check for duplicates before posting, duplicates may be removed
Approved Bots
founded 2 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
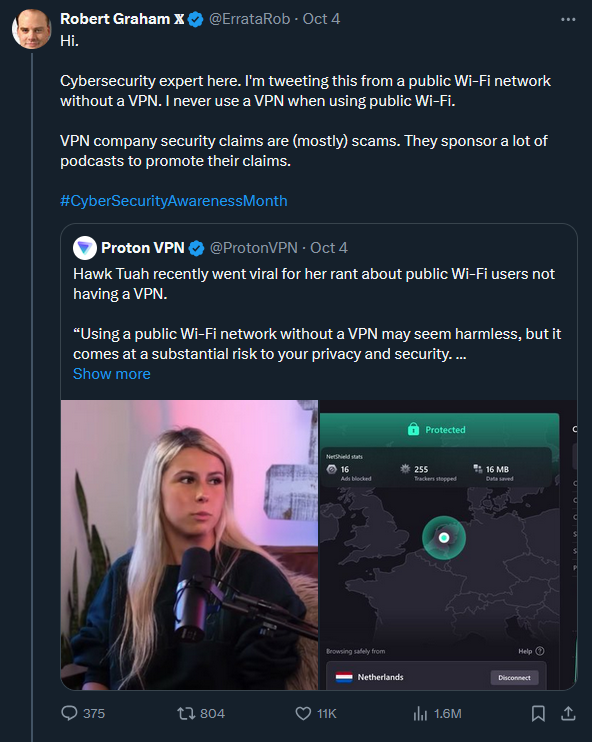
Most VPNs sell themselves on encrypting your traffic to an endpoint that either is in a different locale to get around region locks or to put it out of the grasp of the RIAA so they can’t send your ISP copyright notices.
While remote access to a local network is a good use case for a self-hosted VPN it’s totally unrelated to the use case for commercial VPNs
For the use case of encrypting your traffic while using a public WiFi, both commercial VPNs and self-hosted ones provide the same functionality.
I think the point they're getting at Is that you can't use a self-hosted vpn to hide your piracy activity because the link is registered to yourself.
Yes, but this thread is about security while using public Wi-Fi, which the original comment was saying doesn't require commercial VPNs.
And I highly doubt people are pirating while on public wi-fi, the bandwidth just isn't good enough, and even if it was, it would be a dick move to other public wi-fi users.
Yes that’s true. But also that’s the wink and nudge marketing claim that VPN marketers make while everyone knows the real reason you are using a VPN.
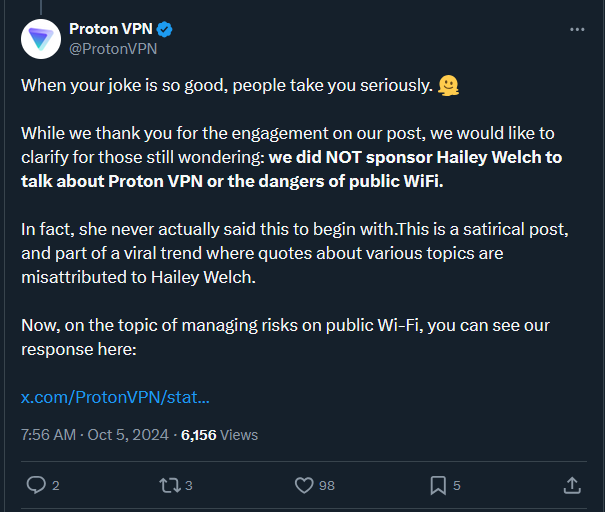
With HTTPS, DNS-over-HTTPS, and most endpoint firewalls dropping non-gateway traffic, the risk is a lot less than the VPN ad reads want you to believe
DNS-over-HTTPS sounds like it'll be the least used by general public since most people I know are still using default DNS settings which would point towards their ISP's. I'm not sure how many ISPs have moved towards DNS-over-HTTPS or if they are even activated by default.
Firefox has DoT enabled by default, maybe Chrome does the same. That would cover the use-case of most people on public wifi.
Wait, it's set in the browser? I've always thought you set that at the OS level.
Both, the browsers (and any other application) can choose to ignore your DNS settings and use whatever other mechanisms they like.
Cool, didn't know that. I'll try and find the setting in the browser.